Contents
- 1 金沢屋 尾頭橋店[張替え 名古屋市中川区]
- 2 クライエール合同会社[空調部材]
- 3 株式会社Y’sHOME[リフォーム]
- 4 青井建工[リフォーム]
- 5 彩蓮電工[電気工事]
- 6 株式会社山幸[板金塗装]
- 7 有限会社スペースイン[リフォーム]
- 8 Select.[土木工事]
- 9 ユニコン株式会社[店舗デザイン]
- 10 石崎電気サービス[エアコン工事]
- 11 HANABIホーム[屋根工事]
- 12 石橋興業[解体工事]
- 13 株式会社信濃インテリア[リフォーム]
- 14 株式会社M&T [リフォーム]
- 15 ミツヤホーム[リフォーム]
- 16 株式会社 シーアンドシー[看板]
- 17 LUFT 株式会社[注文住宅]
- 18 株式会社リモデル・プロ[リフォーム]
- 19 株式会社大野工業所[電気工事]
- 20 福三工業有限会社[エクステリア]
金沢屋 尾頭橋店[張替え 名古屋市中川区]

室内において間仕切りとしての性能を持ちつつ描かれたデザインが楽しめる襖や障子、外からの通気性を確保しつつ虫の侵入を防ぐ網戸、天然素材のい草で作られ調湿性に優れた畳など、建具や内装の新調やリフォームのご依頼を張替え 名古屋市中川区を中心としたエリアで承っています。
押し入れや部屋の間仕切りとして使われている襖は、一般的に木を格子状に組み合わせた組子の上から紙や板などを貼り付けた構造となっています。
近年、ダンボール襖や発泡スチロール襖といった軽量で安価な襖も登場しており、単なる間仕切りとしてだけでなく、襖紙のデザイン性の豊富さから新築で襖を取り入れる方も多くいらっしゃいます。
【金沢屋 尾頭橋店】では様々なデザインの襖紙があり、新しいデザインの襖紙に張替えることでお部屋の雰囲気をがらりと変えることができます。
【会社情報】

■会社名
金沢屋 尾頭橋店
■住所
〒460-0024
愛知県名古屋市中区正木2-13-16
■電話番号
0120-725-203
■営業時間
9:00~17:00
■定休日
日,祝
■HP
https://kanazawaya-otobashi.jp/
クライエール合同会社[空調部材]
 「エアコンの設置を頼みたい」というかたはいませんか?
「エアコンの設置を頼みたい」というかたはいませんか?
メンテナンスなども引き受けてくれる会社があると、何かと頼りになりそうですよね。
そこでご紹介したいのが、大阪 空調部材の「クライエール合同会社」です。
空調部材の販売や、空調のメンテナンスを行なっている会社です。
地域密着型の会社で、小回りの利くサービスが特徴です。
スピーディで高品質の対応が、多くのお客さんから喜ばれていますよ。
難しい要望にも、専門的な知識を活かして対応可能です。
エアコンの稼働に必要な空調部材を豊富に取り揃えているので、さまざまなケースに対応可能です。
「エアコンの修理を依頼したい」「空調の調子が悪い」というかたは、ぜひ気軽に問い合わせてみてください。
【会社情報】

■会社名
クライエール合同会社
■住所
〒572-0084
大阪府寝屋川市香里南之町36-34-914
■電話番号
072-381-9855
■営業時間
8:00~17:00
■定休日
日曜日・祝日
■HP
https://chryair.jp/
株式会社Y’sHOME[リフォーム]
 「今不具合が起きている部分の修繕だけでなく、潜在的な異変がないかどうかチェックしてもらいたい。点検も引き受けてくれる業者があればぜひ依頼したいと思っている。」
「今不具合が起きている部分の修繕だけでなく、潜在的な異変がないかどうかチェックしてもらいたい。点検も引き受けてくれる業者があればぜひ依頼したいと思っている。」
このような方は、総合的なリフォームを行う会社に相談してみてはいかがでしょうか。
埼玉 リフォームで高い評判を誇る「株式会社Y’sHOME」なら、施工と点検の両方に対応してくれますよ。
株式会社Y’sHOMEは一般住宅を中心に、修繕や増改築などを請け負ってくれる企業です。
水回りや外壁の塗装など多種多様な施工を行ってくれるだけでなく、家全体の不具合チェックもしてくれます。
今後修繕が必要になりそうな場所を指摘してくれますから、リフォームのスケジュールを立てるのにも役立つでしょう。
また、近年は日本各地で思わぬ規模の災害が起きています。
災害対策用の施工プランも提案してもらえますので、不安な方はこの機会に相談しておくと良いでしょう。
お問い合わせは電話かメールでできます。
ぜひ一度詳しい話を聞いてみてはいかがでしょうか。
【会社情報】

■会社名
株式会社Y’sHOME
■住所
〒331-0821
埼玉県さいたま市北区別所町52-10-B102
■電話番号
048-796-8753
■営業時間
10:00~20:00(営業時間外でもご相談ください)
■HP
https://yshome21.com/
青井建工[リフォーム]
 リフォームに関する困りごとを、抱えている方も多いと思います。
リフォームに関する困りごとを、抱えている方も多いと思います。
こちらの会社に相談することで、リフォームに関する難しい問題を迅速に解決することができますよ。
プロのスタッフさんがしっかり対応してくれます。
一宮市 リフォームで注目されている「青井建工」では、水回りのリフォームや屋根の塗り直しなどに対応しています。
また、外構工事や間取り変更などの要望にも対応してくれます。
リフォームに関する不安点も、逐一解決して進めてくれるので安心ですよ。
一宮市においておうちのリフォームを視野に入れている方は、ぜひこちらの会社に相談してみてください。
外壁の色褪せや痛みなど、小規模な施工から大規模な工事まで丁寧に対応してくれますよ。
気になる方は、一度ホームページを確認してみてはいかがでしょうか。
【会社情報】

■会社名
青井建工
■住所
〒491-0105
愛知県一宮市浅井町大日比野字東若栗80-1
■電話番号
070-1624-8862
■固定電話
0586-64-7934
■営業時間
9:00~18:00
■HP
https://aoikenko.jp/
彩蓮電工[電気工事]
 電気工事の会社を探している方は、いらっしゃいませんか?
電気工事の会社を探している方は、いらっしゃいませんか?
電気に関する工事を依頼する際には、安心して相談できるスタッフさんが在籍しているこちらの会社に相談してみてください。
さまざまな電気工事の依頼を受注してきた実績があり、安心して相談ができますよ。
大阪市 電気工事で注目されている「彩蓮電工」では、スタッフさんが電気工事に関する資格をしっかりと取得しており、安全に配慮して工事を行います。
丁寧なヒアリングで、要望を叶えてくれますよ。
大阪市において電気工事に関する相談をしたい方は、ぜひこちらの会社に依頼してみてください。
電話だけでなく、メールによる問い合わせも可能なので気軽に連絡ができますよ。
ぜひ検討してみてくださいね。
【会社情報】

■会社名
彩蓮電工
■住所
〒547-0012
大阪府大阪市平野区長吉六反 2-3-47
■電話番号
080-4394-5999
■営業時間
8:00 ~ 17:00
■定休日
日曜日・祝日
※年末年始休暇、夏季休暇
■HP
https://irohadenko.jp/
株式会社山幸[板金塗装]

愛車は長く大切に使っていきたいですよね。
しかし、車は乗っているうちにキズやへこみがどうしてもできてしまうものです。
キズやへこみに対処するためには、鉄金塗装をしましょう。
では、どの業者に依頼すれば良いのでしょうか。
「株式会社山幸」は、群馬県の桐生市で鉄金塗装をおこなっています。
高い技術を持つプロがノウハウを駆使して、愛車を綺麗に仕上げてくれます。
国産車だけではなく、輸入車の対応もできますよ。
バイクや軽自動車、大型車の対応も可能です。
他にも修理や補修、自動車保険に関する相談も対応できますよ。
鈑金塗装 みどり市でお探しの方は、まずはお気軽にお問い合わせしてみてはいかがでしょうか。
【会社情報】

■会社名
株式会社山幸
■住所
〒376-0011
群馬県桐生市相生町1-15
Google MAPで確認する
■電話番号
0277-52-8791
■営業時間
9:00~18:00
■定休日
日曜日・その他不定休
■HP
https://bp-yamakou.jp/
有限会社スペースイン[リフォーム]

諏訪でリフォーム業者を探しているけど、なかなか見つからずお困りの方はいらっしゃいませんか。
リフォーム業者は数多くあるので、何を基準にして選べばいいか迷ってしまいますよね。
では、どこの業者がおすすめなのでしょうか。
長野県の諏訪にある「有限会社スペースイン」では、リフォームをおこなっています。
空間デザインのプロがあらゆるお悩みに応えてくれます。
色彩など細かな部分もこだわるので、納得のいく仕上がりになりますよ。
丁寧なヒアリングとプロデュース力で新築同様の施工も可能です。
また、予算の相談もできるので費用面が心配な方も安心して依頼できます。
諏訪 リフォームでお探しの方は、ぜひお気軽にお問い合わせしてみてくださいね。
【会社情報】
 ■会社名
■会社名
有限会社スペースイン
■住所
〒392-0007
長野県諏訪市清水2-3-30カマクラビルⅢ 302号
■電話番号
0266-57-2121
■最寄り駅
JR中央本線「上諏訪駅」より車で5分
中央道「諏訪IC」より車で10分
■HP
https://spaceinn.jp/
Select.[土木工事]
「住宅の土木工事が得意な業者を探している」というかたはいませんか?
熟練の職人が在籍している会社だと安心して相談できそうですよね。
そこでご紹介したいのが、東松島市 土木工事の「Select.」です。
土木工事や外壁塗装などを行なっている会社です。
丁寧なヒアリングを元に、お客さんの希望を最大限反映できるプランを提案してくれます。
お客さんの数々のお悩みを解決してきた実績があるので、安心して依頼できるでしょう。
近隣住民への挨拶など配慮も徹底して行なっているので、不要なトラブルを避けられます。
「良い職人が揃っている土木工事業者を探している」というかたは、ぜひ気軽に問い合わせてみてくださいね。
【会社情報】

■会社名
Select.
■住所
〒981-0413
宮城県東松島市新東名3丁目1-1
■電話番号
090-8610-7711
■営業時間
9:00~18:00
■HP
https://select-tr.com/
ユニコン株式会社[店舗デザイン]

「ちょっとしたことでも相談できる店舗デザインの会社を探している」というかはいませんか?
出店後でも色々と相談できると嬉しいですよね。
そこでおすすめなのが、宮城 店舗デザインの「ユニコン株式会社」です。
店舗やオフィスのデザインや工事を手掛けているのが特徴です。
何でも相談できる距離感が、多くのお客さんから喜ばれていますよ。
アパレルショップやカフェ、美容室などを、お客さんの要望に合わせて仕上げていきます。
宮城県を中心に、東北エリアや関東エリアまで対応しています。
高い施工技術にも定評があるので、頼りになりそうですよ。
店舗やオフィスの内装デザインで後悔したくない場合は、ぜひ相談してみてください。
【会社情報】
 ■会社名
■会社名
ユニコン株式会社
■住所
〒981-8003
宮城県仙台市泉区南光台1-30-3
■電話番号
022-344-7322
■営業時間
9:00~18:00
■定休日
日曜日・祝日・第2・第4土曜日
■HP
https://unicon1130.com/
石崎電気サービス[エアコン工事]

エアコンに関するお悩みがあるかたは多いです。
設置や修理、メンテナンスなどを全て任せられる会社があると嬉しいですよね。
そこでご紹介したいのが、大田原市 エアコン工事の「石崎電気サービス」です。
コンセントの増設やエアコンのメンテナンスなどを行なっている会社です。
希望があればブレーカーの上限を増やしたりもできますよ。
街の電気屋として地域の方々から愛されている会社なので、安心して工事を依頼できるでしょう。
大田原市を中心とした近隣エリアからの依頼を受け付けています。
ちなみにLANケーブルを通す配線工事も依頼できますよ。
「電気に関するトラブルを抱えている」という場合は、ぜひ一度問い合わせてみてください。
【会社情報】
 ■会社名
■会社名
石崎電気サービス
■住所
〒324-0035
栃木県大田原市薄葉1958‐7
■電話番号
0287-29-2363
■営業時間
9:00~18:00
■定休日
日曜日・祝日
■HP
https://ishizakidenki2363.jp/
HANABIホーム[屋根工事]

「屋根からバタバタと音がする」「屋根から金属板が落ちてきた」というかたはいませんか?
その症状は屋根の劣化を示すサインです。
屋根の劣化によるトラブルを防ぎたい場合は、堺市 屋根工事の「HANABIホーム」の力を借りてみましょう。
屋根の工事を中心に、外壁や内装、水回りなどの工事も行なっています。
施工実績が豊富なので安心して依頼できますよ。
地域密着型の会社なので、ちょっとした不明点や疑問点がある場合も気軽に尋ねられますよ。
屋根は常に風雨や紫外線にさらされている場所なので、定期的なメンテナンスが大切です。
「屋根にメンテナンスが必要かチェックして欲しい」というかたも、ぜひ気軽に問い合わせてみてください。
【会社情報】
 ■会社名
■会社名
HANABIホーム
■住所
〒599-8242
大阪府堺市中区陶器北1389-12
■電話番号
072-200-2846
■営業時間
8:00~18:00
■定休日
日曜日
■HP
https://hanabi-home.jp/
石橋興業[解体工事]

「倉庫や物置の解体工事を検討している」というかたはいませんか?
現場経験が豊富な職人が対応してくれる会社があると嬉しいですよね。
そこでおすすめしたいのが、館山市 解体工事の「石橋興業」です。
解体工事のスペシャリストです。
堅実な解体工事を行なってくれるのが特徴なので、安心して依頼できます。
現場経験が豊富な職人が、納得のクオリティで工事を進めてくれますよ。
地域密着型の会社で、対応の素早さも好評です。
また解体工事以外に外構工事や芝刈り、伐採なども依頼できるので、何かと頼りになりそうです。
「安心して任せられる解体工事業者を探している」というかたは、ぜひ気軽に問い合わせてみてください。
【会社情報】
 ■会社名
■会社名
石橋興業
■住所
〒294-0038
千葉県館山市上真倉2311
■電話番号
0470-28-4499
■定休日
日、祝
■HP
https://ishibashikogyo.jp/
株式会社信濃インテリア[リフォーム]
 大切なマイホームのリフォームは、信頼できる業者にお願いしたいですよね。
大切なマイホームのリフォームは、信頼できる業者にお願いしたいですよね。
調査から施工・アフターフォローまで、ワンストップで依頼できたら安心だとお考えの方はいらっしゃいませんか。
しかし、そんな会社をご自身で探すのも一苦労ですよね。
塩尻市 リフォームの【株式会社信濃インテリア】に相談してみてはいかがでしょうか。
様々な状況に合わせて、高品質で高精度なリフォームを提案しています。
40年以上の経験で培ったノウハウや技術を全て発揮し、より良い暮らしへのサポートが好評です。
リフォームの施工業者をお探しの方は、ぜひ検討してみてください。
気になることや不安な点がある場合は、電話やメールで問い合わせることが可能です。
会社のことがよりよく分かるホームページもぜひチェックしてくださいね。
【会社情報】

■会社名
株式会社信濃インテリア
■住所
〒390-0803
長野県松本市元町2-6-15
■電話番号
0263-36-2367
■営業時間
8:30~17:30
■定休日
第1、第3、第5土曜日 日曜日 祝日
■HP
https://shina-in.jp/
株式会社M&T [リフォーム]

住まいのリフォームにあたって、費用を不安に感じていませんか。
初めてリフォームをするのなら、不安になるのも当然ですよね。
そんな時は無料で見積もりや提案をしてくれる会社まで相談してみましょう。
2008年に創業したのが、枚方 リフォームの「株式会社M&T」です。
水回りリフォーム・ハウスクリーニングなど広く対応しています。
提案や見積もりは無料であるため、費用が心配な方でも安心です。
リフォームの予定があるのなら、ぜひ気軽に連絡してみてくださいね。
安心して暮らせる住まいづくりを、丁寧にサポートしてくれます。
予算も含めてベストな提案をしてくれますので、おすすめの会社ですよ。
【会社情報】

■会社名
株式会社M&T
■住所
613-0036 京都府久世郡久御山町田井東荒見50-3
■電話番号
0774-66-7111
■営業時間
9:00~18:00
※土曜日のみ17:00まで
■定休日
日
■HP
https://mandt-corp.jp/
ミツヤホーム[リフォーム]

経年による住まいの劣化にお悩みではありませんか。
建ててから年数が経つと、設備が劣化して使い勝手が悪くなってしまいますよね。
使い勝手の悪さで悩んでいるのでしたら、ぜひ住まいのリフォームを検討してみましょう。
熊本市 リフォームの施工を行っているのが「ミツヤホーム」です。
リフォームを相談すると、予算に合わせたプランを立案して提案してくれます。
内装だけでなく、外壁塗装や屋根の点検などへの対応も可能です。
リフォームを検討しているのでしたら、まずは気軽に相談してみてくださいね。
家の状態を丁寧に診断したうえで、相談者にとって適切なプランを提案してくれます。
熊本でリフォームを考えている方にとって、頼れる相談先ですよ。
【会社情報】
 ■会社名
■会社名
ミツヤホーム
■住所
〒861-8039
熊本県熊本市東区長嶺南7丁目1−8
■電話番号
096-240-2849
■営業時間
9:00~18:00
■定休日
火曜日
■HP
https://mitsuya-home.jp/
株式会社 シーアンドシー[看板]
「古くなった看板をリメイクしたい」とお考えではありませんか。
看板は、店舗にとっては非常に重要なものですよね。
古くなったり壊れたりしている看板があるなら、まずは専門の業者に相談してみましょう。
埼玉 看板の設置や撤去なら、「株式会社 シーアンドシー」の幅広い対応が好評です。
作業内容や費用などに納得してから作業を進めてくれます。
出張費用や見積もりには費用がかかりません。
看板の修理やリメイクをしたい時は、ぜひ遠慮なく相談してみてくださいね。
不要になった看板の撤去や処分などにも対応してくれます。
看板について相談したいと考えているのなら、おすすめの会社ですよ。
【会社情報】
■会社名
株式会社シーアンドシー
■住所
〒357-0021
埼玉県飯能市双柳1148-24
■電話番号
050-1127-1636
■営業時間
9:00~17:00
■定休日
土曜日・日曜日・祝日
■HP
https://cc-office.jp/
LUFT 株式会社[注文住宅]
 「自然と調和する注文住宅を建てたい」というかたはいませんか?
「自然と調和する注文住宅を建てたい」というかたはいませんか?
世代を超えて愛されるような家を建てられると嬉しいですよね。
そこでご紹介したいのが、真庭市 注文住宅の「LUFT 株式会社」です。
世界基準の設計を採用している工務店です。
完全オーダーメイドではないものの、立地条件や周辺環境を徹底的に調査し、その場所に合った設計を行なうのが特徴です。
お客さんの意見を取り入れつつ、一流の専門家がプロデュースを行ないます。
お客さんの要望に合わせて、最適なプランを提案してくれますよ。
住み心地にこだわっているのも特徴で、アフターフォローもバッチリです。
「匠の技が光る注文住宅を建てたい」というかたは、ぜひ気軽に相談してみてください。
【会社情報】■会社名
LUFT 株式会社
■住所
〒719-3204
岡山県真庭市惣259-1
■電話番号
0867-42-7177
■営業時間
10:00~18:00
■定休日
木曜日
■HP
https://luft-okayama.jp/
株式会社リモデル・プロ[リフォーム]
 「高齢の家族がいるので、バリアフリーリフォームを行ないたい」というかたはいませんか?
「高齢の家族がいるので、バリアフリーリフォームを行ないたい」というかたはいませんか?
バリアフリー工事の実績が多い会社だと安心して任せられるでしょう。
そこでおすすめしたいのが、つくば市 リフォームの「株式会社リモデル・プロ」です。
安心安全で快適に暮らせる家づくりを行なっているリフォーム会社です。
お客さんへの丁寧なヒアリングを通して、満足できるリフォームやリノベーションを行なってくれます。
国土交通省の「住宅リフォーム事業者団体登録制度」に登録された優良会社ですよ。
定休日の水曜以外は9:00〜18:00まで相談可能です。
店舗での相談のほか、電話やメール、お問い合わせフォームからでも相談できますよ。
「信頼できるリフォーム会社を探している」というかたは、ぜひ一度問い合わせてみてください。
【会社情報】 ■会社名
■会社名
株式会社リモデル・プロ
■住所
〒300-1231
茨城県牛久市猪子町995-209
■電話番号
0120-207-301
■営業時間
9:00~18:00
■定休日
水曜日
■HP
https://remodelpro.jp/
株式会社大野工業所[電気工事]
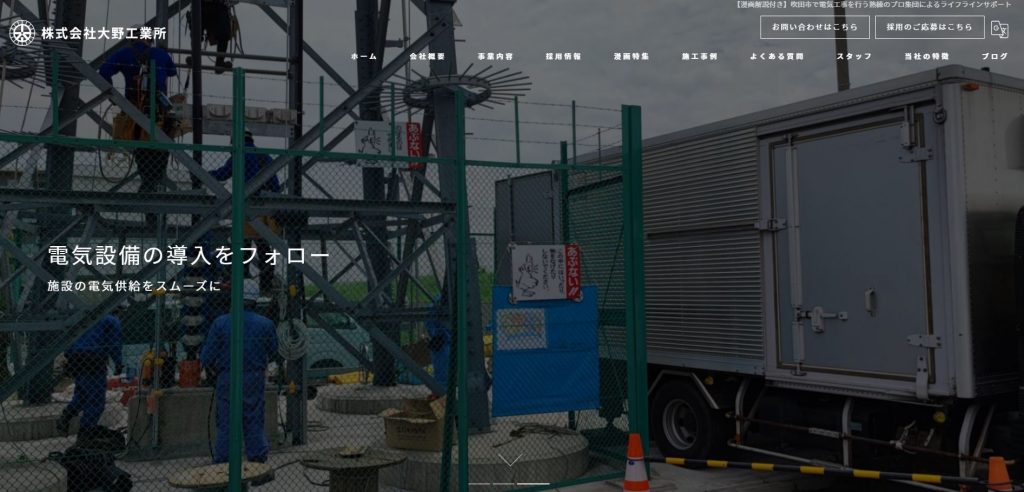 「電力供給設備を新設したい」という場合、どの会社に相談すれば良いのでしょうか?
「電力供給設備を新設したい」という場合、どの会社に相談すれば良いのでしょうか?
施工実績が豊富で評判の良い会社があると嬉しいですよね。
そこでご紹介したいのが、吹田市 電気工事の「株式会社大野工業所」です。
既存の電力供給設備のメンテナンスや新規設備の導入を行なっている会社です。
高品質な工事を行い、安定した電力供給を実現させます。
迅速で丁寧、かつ安全に工事を行なってくれますよ。
些細なことでも相談できる、頼りになる存在です。
吹田市はもちろん、日本全国に対応しているのも特徴です。
工事ごとに丁寧に細かいチェックを重ねるので、トラブルを未然に防ぐことが可能です。
電気工事を検討中のかたは、ぜひ一度相談してみてください。
【会社情報】 ■会社名
■会社名
株式会社大野工業所
■電話番号
06-6385-0702
■所在地
〒564-0044
大阪府吹田市南金田2-6-3
■設立
1985年6月
■代表取締役
大野 俊英
■資本金
1000万円
■従業員数
5人
■定休日
日曜日
■取引先
株式会社K E S
■HP
https://onoko-denki.com/
福三工業有限会社[エクステリア]
 「庭をもっとおしゃれにしたいのだけど、イメージが湧かない…」というかたはいませんか?
「庭をもっとおしゃれにしたいのだけど、イメージが湧かない…」というかたはいませんか?
施工プランを色々と提案してくれる会社があると良いですよね。
そんなかたにおすすめなのが、横浜 エクステリアの「福三工業有限会社」です。
エクステリア工事や外構工事全般を行なっている会社です。
門扉やフェンス、玄関アプローチ、ガレージなど、さまざまな箇所のリフォームが可能です。
「もっとおしゃれにしたい」「防犯対策をしたい」というように、お客さんの要望に合わせて柔軟に対応してくれますよ。
今あるカーポートの補修なども行なっています。
熟練の技術を持つ職人が施工してくれるので、仕上がりに満足できるでしょう。
「庭をおしゃれにしたい」「ガレージを設置したい」といった要望があるかたは、ぜひ気軽に相談してみてくださいね。
【会社情報】 ■会社名
■会社名
福三工業有限会社
■電話番号
045-472-0798 (優先) / 090-3248-8710
■FAX番号
045-472-0689
■所在地
〒224-0042
神奈川県横浜市都筑区大熊町81
■営業時間
7:00 〜 19:00
■定休日
日曜・祝日
■事業内容
建設業、外構工事(ガレージ、フェンス、擁壁、土間、アルミ屋根)
■保有資格
建設業許可 神奈川県知事許可番号第85934号
■HP
https://fukumi-kougyo.com/